AARP Hearing Center
According to a 2019 AARP study, people are more likely to respond to threatening scam messages than to those that promise rewards. That might explain the growth of email extortion scams that threaten to publicize compromising information about you — true or not — if you don’t make a quick payment.
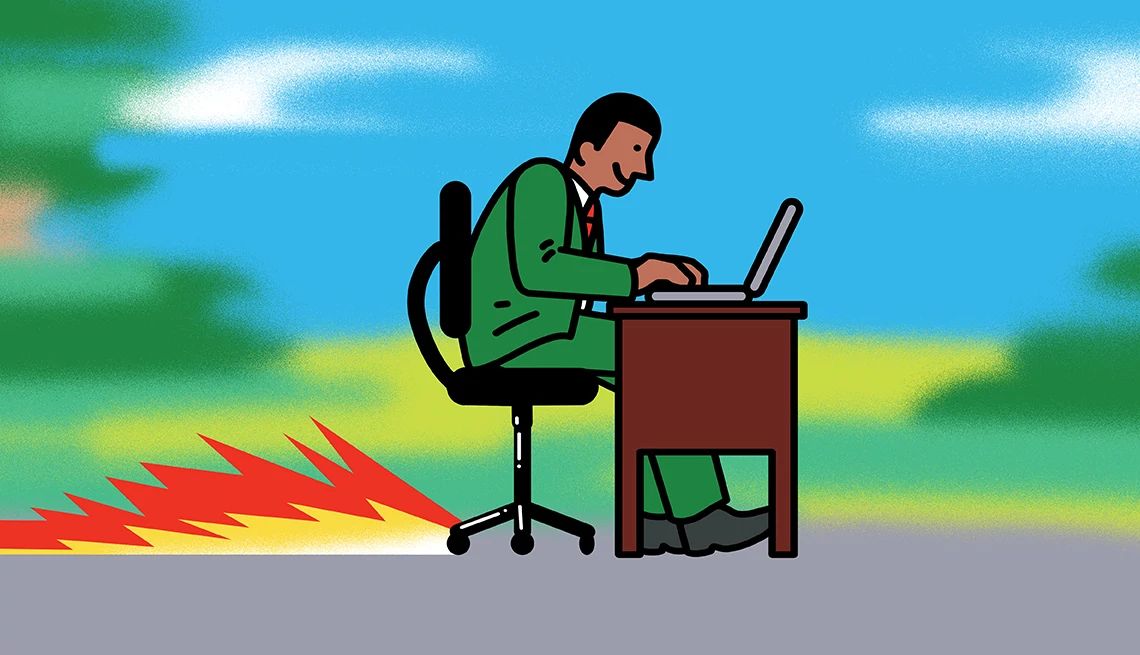
Extortion scammers have a valuable scare tactic at their disposal: They show in their messages that they know a password you’ve used for online accounts. They claim they’ve implanted malware on your computer that lets them capture your keystrokes, watch through your webcam and amass evidence that you, say, frequent adult websites. And they say they’ll share that information with all your email and social media contacts — perhaps with a video of you enjoying your viewing — unless you pay hush money, typically several hundred dollars in the form of Bitcoin.
Don’t panic. There’s little chance the cyber-blackmailer has really invaded your computer. Extortion scammers send out threats indiscriminately, using big batches of email addresses and associated passwords that they likely obtained on the black market following big corporate data breaches. They hope to stumble across a few people who don’t change their passwords regularly or do have some secret they don’t want known. That there have been actual cases of hackers gaining access to people’s webcams gives the scam a veneer of plausibility.
To make it even more intimidating, some scammers tinker with their email messages, filling in the “From” section with your actual email address to create the illusion that they have control of your account.
This ruse is rampant. Cybersecurity company Symantec says its software blocked almost 289 million extortion emails in the first five months of 2019. When the message does get through, it can be lucrative. The FBI’s Internet Crime Complaint Center (IC3) documented 43,101 cases of online extortion in 2019, with victims suffering losses of $107.5 million.
The pornography scenario, termed “sextortion,” accounts for a large share of email extortion complaints, and these have spiked amid the coronavirus outbreak as people are spending more time at home and online, according to the FBI. Online extortionists might also claim to have caught you in a different sexually compromising situation, like cheating on your spouse, or even to have planted a bomb at your workplace.





























































More From AARP
About AARP Fraud Watch Network
Helping the consumer avoid identity theft, dating scams, tax fraud and moreAARP Fraud Watch Network Helpline: 1-877-908-3360
Our toll-free service is available Monday through Friday, 8 a.m. to 8 p.m. ET
Find and Report Scams Near You
Stay up-to-date on fraud in your community using AARP's Scam-Tracking Map. Search for scams by zip code or report a scam near you.