AARP Hearing Center


BRETT JOHNSON IS AN IMPOSING and charismatic ex-con whom the U.S. Secret Service once dubbed the “Original Internet Godfather.” His criminal masterstroke? Creating “Shadowcrew,” one of the first online forums where bad guys could safely buy guns, stolen credit cards, Social Security numbers and every drug imaginable. But Shadowcrew was shut down by federal agents in 2004, and for the next decade Brett was in and out of prison. At one point he went on a four-month run from the law, funded by roughly $500,000 he stole from ATMs. That landed him on the Secret Service’s “Most Wanted” list.
He’s the good guy of our story.
As is Blue London. Wiry, in his early 20s, with hair to his waist and an attitude to match, Blue recently pleaded guilty to crimes related to his role as a hacker for some of the biggest illegal sites on the internet. It was his first job and, with a looming prison sentence, it may be his last for a while. To protect him from reprisals, we agreed not to use his real name; he asked that we use “Blue London.”
Brett and Blue have seen the light. Today, both are willing to share in detail how the internet gets used by criminals to steal money from you. Brett, because it’s his new job: He is now a consultant who helps law enforcement catch cybercriminals. Blue, because he wants to reduce his prison sentence.
Their coming forward is timely. Massive data breaches get big headlines, but many more occur with little fanfare. In 2017, there were 829 data breaches in the United States, exposing over 2 billion individual records, says Paul Stephens of the Privacy Rights Clearinghouse. Identity fraud — defined as using personal identifying information to steal money from victims — is at an all-time high, with 16.7 million Americans losing nearly $17 billion in 2017, according to Javelin Strategy & Research. Brett and Blue know why these numbers keep growing because they contributed to it. And truth is, it was pretty easy.
The two recently gave me a tutorial on how criminals go about stealing people’s identities and turning that data into money. The class took place mostly in the “dark web,” a secretive place on the internet where crooks and scammers buy and sell their wares under the protective blanket of anonymity. Here’s what I discovered.
A Decent Into the Dark Web
Think of the internet as an ocean. At the top is the “surface web” and its familiar occupants like Google, CNN, Amazon, Yahoo and thousands of other public websites. The surface web is where the vast majority of people spend their internet time. All is public, all is searchable, and all is (mostly) friendly.
Go a little deeper, where the sunlight begins to fade away, and there is the “deep web.” It is much larger than the surface web but can only be accessed by individuals who have logins for the databases and websites here. Most of the activity is perfectly legal; it’s just not as easy for everyday folk like us to see. Some of the biggest sites here include the databases for NASA, the U.S. National Oceanic and Atmospheric Administration, the U.S. Patent Office and private databases like LexisNexis and Westlaw. Traditional search engines can’t find these pages because they aren’t indexed like pages on the surface web; you need to know your destination and have an authorized password to get in.
Descend even further, to where there is no light and far fewer denizens, and there is the dark web (also called the “darknet”), a part of the deep web that is accessible only to those who use software called TOR, which stands for The Onion Router. Ironically, TOR software was developed by the U.S. Navy in the 1990s as a way to allow intelligence agents operating overseas to communicate anonymously with their colleagues here in the U.S. It was released as free, open software to the public in 2003, though government dollars continued to support its upkeep and growth.
The Onion Router got its name because all transmissions through it are anonymous: Messages are sent to multiple servers around the world to disguise the sender — kind of like layers of an onion. Search for information using TOR, and it takes several seconds to load, because your request travels tens of thousands of miles between all those servers before coming back to you. It’s perfect for preserving anonymity for political dissidents, journalists, spies and — as it turns out — criminals. TOR is free and available to anyone who wishes to download the appropriate software onto his or her computer.
Criminals have flocked to the dark web because it allows the buying and selling of illicit goods with total anonymity. The TOR browser hides users’ IP addresses, and transactions are usually conducted in a cryptocurrency like bitcoin to make them untraceable.
How big is the dark web? No one knows exactly. But consider AlphaBay, a site on the dark web that was taken down in July 2017 by the FBI. At its peak, AlphaBay had over 200,000 users and was taking in between $600,000 and $800,000 a day. The site’s founder, Alexandre Cazes, was arrested; eight days later he was found dead in his jail cell from an apparent suicide.
While most of the illegal traffic on AlphaBay was drug related, there was also a huge volume of so-called digital goods sold. The FBI estimated that when AlphaBay was busted, it had listings for 4,488 stolen personal IDs, 28,800 stolen credit card numbers and 3,586 hacking tools. Attorney General Jeff Sessions called the bust “the largest darknet marketplace takedown in history.”
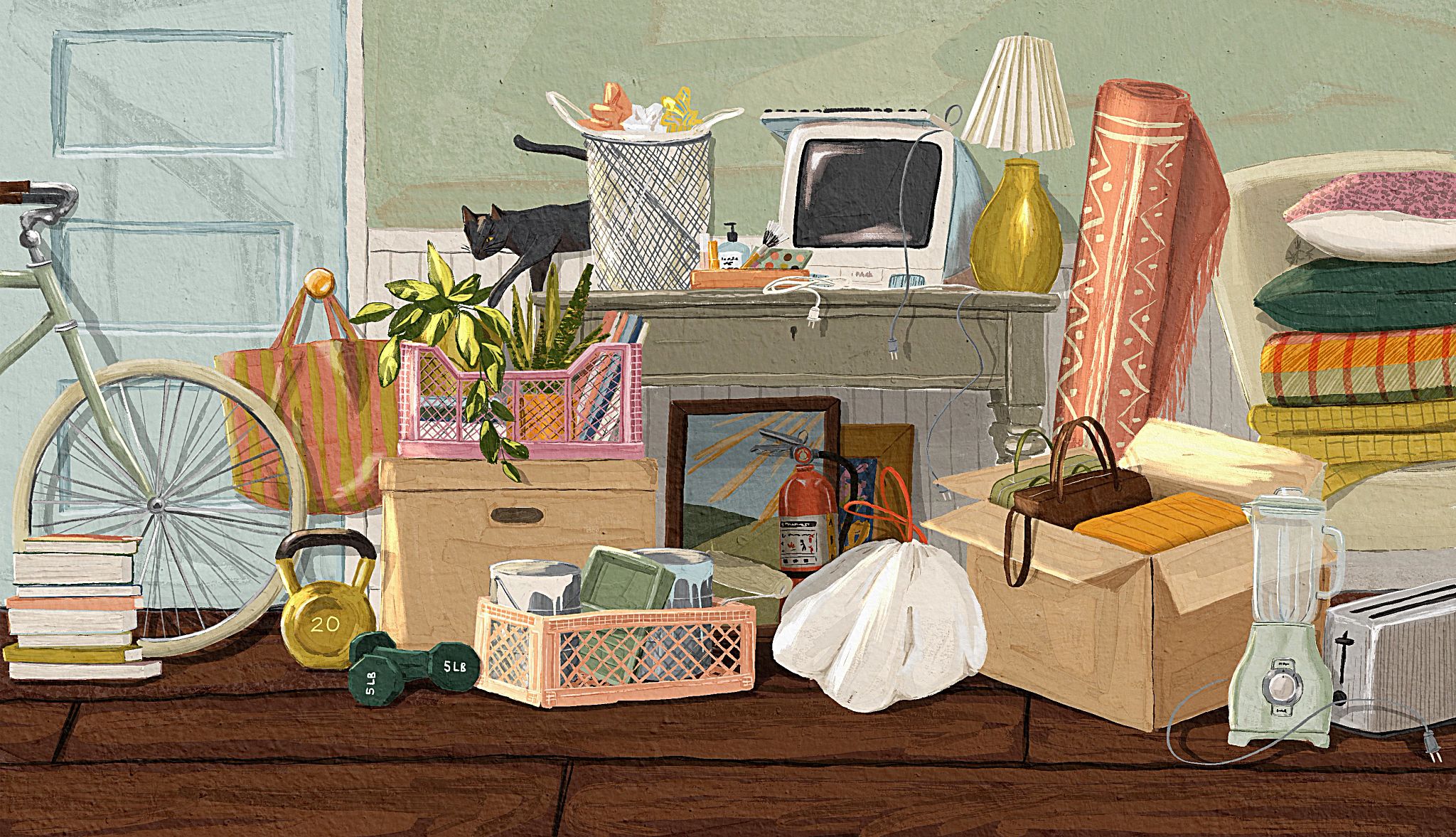
A Rich Marketplace
But there are plenty of other inhabitants of the dark web eager to fill the space that AlphaBay vacated. Brett and Blue showed me several dark web sites that were selling a range of stolen digital goods: high-end credit card numbers, logins and passwords, individual credit reports and what is known as a “fullz” — a complete package of everything needed to commit identity theft: Social Security number, date of birth, mother’s maiden name, address, phone numbers, driver’s license number and more.





























































More From AARP
Quiz: Protecting Yourself From Identity Theft
Test your fraud-prevention savvy