AARP Hearing Center
Subscribe: Apple Podcasts | Google Play | Spotify | Stitcher | TuneIn


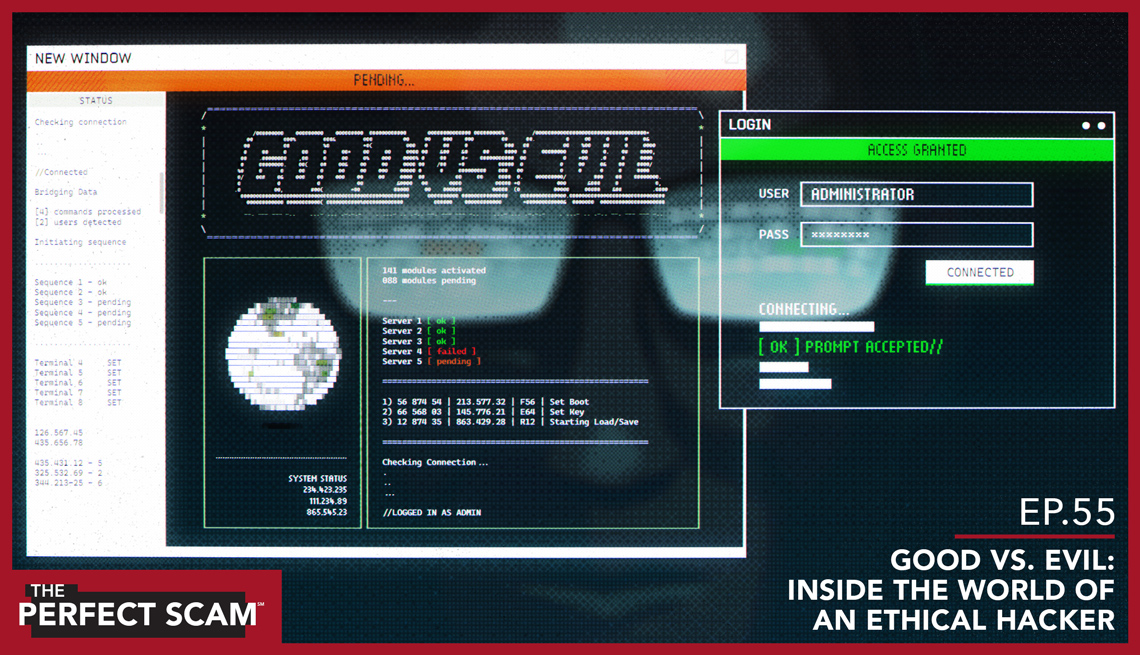
[00:00:00] Julie: This week on AARP's The Perfect Scam.
[00:00:04] The bad guys do exactly what they want. They know exactly what they're targeting, and that's infinitely harder to protect yourself from.
(MUSIC SEGUE)
[00:00:14] Julie: Welcome back to AARP's The Perfect Scam. I'm Julie Getz, and with me today is my cohost, Frank Abagnale. Frank, it's always great to see you.
[00:00:23] Frank Abagnale: Great to be here. Thanks, Julie.
[00:00:24] Julie: Frank, on this episode, we're going to talk about hackers, but not the ones we typically think about typing feverishly on their keyboards and breaking into computer systems around the world, but the other ones, what businesses refer to as ethical hackers. Can you please explain what an ethical hacker is and what do they do?
[00:00:40] Frank Abagnale: An ethical hacker is somebody who really knows how to use their talent, their ability in the right way to help companies know if there's intrusion software on their system, if there's malware on their system. They think like the criminal. They don't look at it as the guy who got a degree in computer science; they're looking at it as somebody who really knows how to do these things, so they know how someone would try to get into that company, and they're able to find a lot of flaws in their system, close down those flaws, know if there are hackers, how to keep the hackers out of the system or get them out of the system.
[00:01:12] Julie: So how do you become an ethical hacker? Do you have to have a criminal background?
[00:01:16] Frank Abagnale: I get a lot of calls and emails and letters from people in prison, and they send me some clippings with the letter, and they say, look, I was a great hacker, and I'm getting ready to come out of prison in six months, and I'd really like to do kind of like what you did with your life, turn my life around and go to work for a company and help them detect soft spots in their system. And I explain to them, that's well and good, but you really have to earn people's trust. You can't expect that some company's going to hire you out of prison the next day because you're a good hacker and say, yeah, look into my system and see if there's some problems with it. That takes a lot of time. It took me years to get the FBI to trust me, for agents to trust me; a long, long period of time. So it's good to have ethical hackers, because it's an instinct that people have.
[00:02:02] Julie: Absolutely. Well Frank, thank you. How about we get into this interview with Jason Glassberg, CEO of Casaba Securities who shares with us how the business of ethical hacking works for him and what sort of security threats he sees on a daily basis, and of course, why business it thriving for him right now.
(MUSIC SEGUE)
[00:02:22] Julie: Good morning, Jason. It's Julie Getz with AARP's The Perfect Scam. How are you?
[00:02:26] Oh, I'm very good. How are you doing today?
[00:02:28] Julie: Meet Jason Glassberg. He's a professional hacker. Companies hire him to break into their security systems and help make them fool-proof so real fraudsters can't get in. I can't help but imagine Jason sitting in a cold, dark basement surrounded by computer monitors and keyboards hacking away into the world's most elite security systems. I mean, isn't that what we all see in the movies? Well, it turns out that's not what Jason's like at all.
[00:02:54] Julie: It's pretty early out on your side of the coast, isn't it?
[00:02:56] Jason Glassberg: Ah, it's not so bad. I've got kids to go to school, so I've been up for a couple of hours.
[00:03:00] Julie: Okay, so Jason's not only a professional hacker, he's a busy dad with four kids. He's also a Seattle Seahawk enthusiast. This all makes him a lot less scary. Frank explained that some hackers get their expertise from their criminal background, but Jason, he made his way into ethical hacking on a very different road.
[00:03:19] Jason Glassberg: I always was interested in computers. I came from the age when the PC just started hitting the mainstream, but I went to school and actually took a degree in classical archeology, but always maintained my love of computers and joined up with a group of other computer enthusiasts back in the '90s when the web just started really blossoming, and we started doing testing for large consulting companies regarding computer security. And it was kind of interesting to be part of the group of folks who started developing this process and turned it into a legitimate kind of way for software companies to test their software. It's been really interesting to see how the acceptance of this line of work has matured and has now become kind of an accepted part of the development process.
[00:04:16] Julie: Jason, we uncover a lot of shocking scam stories in our podcast, and at times it feels like we'll never be able to protect ourselves from these relentless fraudsters ever again. How are folks like you helping keeping us safe?
[00:04:28] Jason Glassberg: There's really two ways to look at the whole world of security. There's the reactive: I have a software company, and I've developed an application. I want people to come, make sure that there are no hidden holes, or folks who are not authorized to take advantage of the systems. And that's one way that we would engage with the client. The other way is a more proactive process, which basically says, how do I think about security before I even build something? What are some of the pitfalls I should be considering as I'm designing something? And that's really the future, and that's what we have been working much more diligently on, is providing a more proactive view of this so software companies know the pitfalls before they ever design anything.
[00:05:15] Julie: What are some of the projects that you're working on now? Are you allowed to tell us about them?
[00:05:18] Jason Glassberg: Right now, we're very actively involved in medical devices, because the FDA has instituted a requirement that all medical devices that are going to be sold to the public have to go through a very rigorous course of security testing, and it's exciting and fun stuff, and it's nice to see an area where the US is leading the world in terms of security.
[00:05:47] Julie: And why is security so important for medical devices?
[00:05:50] Jason Glassberg: Well, there's been an incredible increase in the amount of connectivity between all these devices, which is awesome for the patient, right? You can have an MRI done at a hospital in some rural community and have those results sent back to a much larger hospital in the big city, and have the benefit of, of more specialized doctors be able to look at that information; or you can be hooked up to a machine that provides insulin at a certain regulated amount and be monitored by a nurse just as the internet connected at your house. But for every benefit there's a kind of a, an equal dark side. And so we want to make sure that when these MRI images are sent back to a hospital that no one can intercept them, and we want to make sure that when someone's monitoring some insulin pump, or some heart machine, that those machines can't be monitored by someone else, right? Basically we want to be able to keep confidential information from the patient to be as secure as possible.
[00:06:55] Julie: Got it. That sounds very helpful, particularly with the aging population. All of this is so important.
[00:07:01] Jason Glassberg: Well absolutely. It's just an incredible benefit. All of this interconnectivity that's blossomed in the last 10 years is just an enormous benefit to everyone. I mean, so many people can now keep in touch, and all of these devices that we're able to connect, it's just terrific, but, you know, people just need to keep their wits about them and understand that there's always a downside. And so, you just need to be able to protect yourself and be assured that you have a certain sense of privacy. And that's ultimately what we try and do in our field.
[00:07:31] Julie: Interesting. Since you see more of the dark side than we do, how does that change your perspective on security?
[00:07:37] Jason Glassberg: One of the things that is pretty apparent, is folks have kind of an interesting perception of what it is to be secure. They think of their systems like a castle or a fortress with a big gate and a big guard door and towers, so a very hard outer crust, but they don't necessarily protect from within. So if someone's allowed to get past that castle, maybe they dig a tunnel underneath the walls or maybe they float a boat in a moat and somehow figure out to get in, all sorts of damage can be caused. And that's the kind of thing we come across all the time, is that people go to great lengths to protect their outer um, defenses, but they don't have a consideration of what happens when people break in through those defenses.
[00:08:27] That's really interesting to learn about big businesses. And I'd like to transition to learning how security impacts our listeners, and particularly for our listeners who do a lot of traveling. Do you have any tips on how people can better protect themselves from becoming a victim to a scam when they're on vacation?
[00:08:43] Jason Glassberg: You know, one of the things that is unfortunate in life is that bad guys tend to know when good folks have their guards down. And one of the times traditionally people have their guard down is when they're traveling; you're going on vacation, you're happy to be away, and you're not necessarily thinking how am I going to protect myself? And unfortunately this is the kind of attitude that some of the bad guys will take advantage of. And the way they do this is a number of ways. A lot of times people go and just go to a hotel and don't even think twice about using the hotel wireless. The hotel provides a wireless, they provide a, a password, if it's got a password, it's got to be safe, and they go and they log in and you might do some banking, you may want to transfer funds, you may want to buy some stuff, but of course, you're on a, an unknown network, and you don't know who necessarily is listening on that network, and so we oftentimes warn folks, you know, unless you can be assured of the security of the network, which is very hard to do, you're better off either using your own personal device connected to your cell phone doing a tether, or waiting till you get home to do any kind of financial transactions on a network.
[00:10:02] Julie: What about using your credit card?
[00:10:03] Jason Glassberg: You often need to be very careful using your credit card, because there are number of scams involved in stealing your credit card information from you as you're traveling. There are things like card skimmers, where you can go and folks put another device within the, the reader of a gas station or an ATM which is secretly reading the codes off your magnetic strip and transmitting them to the bad guy, and so, you know, a piece of advice there is don't use an ATM in the back of a gas station for example; uh, take the time to go to a bank. Also, we tend to recommend that folks use a credit card specifically reserved for traveling, and that way it's a lot easier to see if some unknown charges happened on your trip. If you use a credit card for everyday activities, in addition to your travel, it may be hard to see if someone's put an unnecessary or unwanted charge on your card.
[00:10:57] Julie: Jason, is one smart device safer than the other for when using wi-fi when you're traveling, and are there any other lurking dangers that we should be aware of?
[00:11:06] Jason Glassberg: Well, I think the bottom line is that all of these devices are essentially the same, meaning that you're not really safer using your phone or your tablet than you are using your PC, and this is kind of a, a thing we run across all the time. Oh, but my phone's safer, but that's not the case, because many times what you're doing on your phone is going on the web, and going on the web to a bad website can be equally devastating to you on the phone as it can be for a tablet, just as it can be on a PC, and when your phone connects to a wi-fi, it's the same danger as if your PC connects to a wi-fi. Unless you can assure yourself that this is a secure wi-fi, you're best off not using it.
[00:11:51] Julie: In your line of work, do you see scams on a daily basis?
[00:11:54] Jason Glassberg: We do but interestingly, we work at a very technical end of this business. We look at deep dives into people's programs. We do incredibly detailed surveys of network infrastructures, but ultimately, the thing that always gives up the goods is the human element. And so, what we mostly caution folks and look at are a lot of these spam emails and malicious websites that happen when you click on links that you get when you get these emails.
[00:12:27] Julie: What typically happens when somebody clicks on one of those links?
[00:12:30] Jason Glassberg: Typically what happens is that you're redirected to a website that will either do one of two things. One, it can put malware or a bad piece of software in your machine that potentially can load things like a keyboard logger which will capture all your keystrokes, or put in a back door which creates a way for folks to come into your PC and operate it and steal data off it without your knowledge; so that's one way. So people can install these bad pieces of software in your machine. The other thing that can happen is that you get redirected to a website that looks awfully similar to either a banking site or a e-commerce site, and they ask for things like, oh, can we just have your user name and password to log on, or hey, can you please enter your credit card information to confirm this or that, and of course, at that point you've given up the goods and the bad guys win.
[00:13:27] Julie: Is there a way that you can describe the type of criminals who are trying to steal information from people?
[00:13:32] Jason Glassberg: You've got the analogy of the car thief, right. So you've got two kinds of car thieves. You've got the guys who are basically going up and down the block looking for cars that have keys left in the ignition and their windows rolled down. And that's kind of one classification. The other is the more targeted approach. They're looking for parts for a 1993 Honda Accord, and they go in and they find a 1993 Honda Accord and they steal that particular car, and of course, in that case, the bad guys know exactly what they want, they know exactly what they're targeting, and that's infinitely harder to protect yourself from. So really, what you want to do is not be the person who has their windows rolled down and leaving their keys in the ignition. And doing things like not randomly clicking on websites, not using unprotected wi-fi, keeping your computer up to date with the latest versions of the operating system and web browsers, and all the other programs that you use, and running anti-virus are ways that you basically make it more difficult for the bad guys to attack you and move on down the road looking for that person with the windows rolled down and the keys in the ignition.
[00:14:44] Julie: Those are all really good tips, and I love that analogy. Is there anything I didn't ask you that you may want to share with our listeners?
[00:14:51] Jason Glassberg: The only thing I can think of is that for all of these fabulous technological benefits we see, there's always, as I mentioned, a downside, and so the things that are the most convenient and the easiest to use may not necessarily be the most secure. And so devices and systems that are the most secure may not necessarily be the easiest to use. And so it's really up to the individual to decide what level of security versus convenience they're willing to accept.
[00:15:23] Julie: All right. Well, thank you so much and enjoy the rest of your day, Jason.
[00:15:27] Jason Glassberg: All right, thank you so much.
(MUSIC SEGUE)
[00:15:33] Julie: Now I'm back with my cohost, Frank Abagnale. Frank, it sounds like most of the companies that hire Jason are big corporations. For our listeners that own their own small businesses, is there any benefit to considering the services of an ethical hacker?
[00:15:47] Frank Abagnale: Big corporations can afford to have the best technology in place, have the best people in place, the best IT department, but there are a lot of medium-sized, small companies that can't afford to have all of that technology in place. They also sometimes unfortunately believe, well that'll never happen to me, I'm just a small business over here with this. And here's the scary part, they have so much more to lose than the big company. First of all, the big company many times has uh cyber insurance, so if they had a loss of a million dollars, they pay the $200,000 deductible and then they get the insurance company to cover their loss. But if you and I own a small business and we had 15, 20 employees, someone hacks into our system and causes us a tremendous loss, we're out the money. We're out of business. We don't have the money. So small businesses who actually are attacked more than big businesses because big businesses are harder to attack, have a lot more to lose. I think it's very important that companies understand between now and 2021, we expect that there'll be more than 6 trillion dollars in cyber fraud type crimes, so it's very important today to understand that that's your number one threat is the outsider trying to get into your company and steal information and steal data, and whatever else they can do: trade secrets, etc. So every company should, whether no matter how big or how small they are, they should be asking themselves, what am I doing to protect the information in my company?
[00:17:13] Julie: Those are all excellent points, Frank. I wanted to ask you, earlier in the show, Jason talked about the dark side of technology. How do you see this dark side showing up?
[00:17:22] Frank Abagnale: The more things we say about ourselves, the more things we tell people, then the more things people are able to find out about us. People ask me the question all the time, "So, Frank, when they target these seniors, for example, how did they know the man at that phone number or that man at that house is 80 years old or, or he's 30?" Well, when I was a kid, you went to the phone book, it gave you someone's name, phone number, and address. Now you go to WhitePages.com; it tells you who lives in the house, the age of the people that live in the house, the relationship to the people that live in the house. So if I take that data and then I combine it to their zip code and their address, I can take those pieces of information and really direct them to a wealthy neighborhood or area, and I know the person I'm calling is a person in their 80s or a person in their 70s. So this is all part of that too much information. There's no reason to know all of that, and yet, people don't understand that, but you think it's a convenience to give that information, but to a criminal, that's just a gift.
[00:18:22] Julie: Wow. Would you say that we should be alert to potential hacks in the devices we use at home as well?
[00:18:26] Frank Abagnale: You think about even your home, your television, your remote control to your television that you talk to, the device that you ask, "What's the weather today, order me this from uh Amazon," all those devices can be easily manipulated and hacked into; your security cameras around the property of your house, your refrigerator that tells you whether you have, need a new, you need to order some milk to put in your refrigerator. I don't need my refrigerator to talk to my toaster. They've been getting along great for years and years without having a conversation. So sometimes we have too much technology, unnecessary technology. So many companies today develop those technologies, and then they want to turn around and put them out in the marketplace without ever asking that very serious question, okay, this is great, but how would someone misuse it?
[00:19:13] Julie: And we've mentioned on this show before, but can you talk about it again briefly, the benefits to freezing your credit. I understand that Congress has actually made it easier to do this.
[00:19:22] Frank Abagnale: Last year, Congress passed the law that prohibits credit bureaus now from charging you a fee to freeze your credit. There's no fee. You can unfreeze it, refreeze it a million times; there's no fee associated with it. Once you've done it, you never have to do it again. Then, if for some reason you're going to go buy a car this weekend, you walk into the car dealership, you say, "Look, I'd like to finance this car for three years, I'd like to get the best interest rate from the best bank, and you unfreeze your credit to the dealership so the dealer can run the credit through the banks, and as soon as your credit approved, your credit, credit's frozen uh back again. So today, everyone should freeze their credit.
[00:20:01] Julie: And just so we're clear for our listeners, the law states you can freeze your children's credit as well. There's no age minimum to have your credit frozen, so listeners, if you're interested in freezing your credit so a thief can't open a credit card account in your name or take out a mortgage or buy a car, get in touch with each of these three credit reporting bureaus: that's Equifax, TransUnion, and Experian. All right, well Frank, thank you so much. Once again, we have Frank Abagnale, and we'll see you next week.
[00:20:27] Frank Abagnale: Okay, thank you.
(MUSIC SEGUE)
[00:20:30] Julie: If you or someone you know has been the victim of a fraud or scam, call AARP's Fraud Watch Network Helpline at 877-908-3360. Thank you to our team of scambusters, Producer Brook Ellis, our Audio Engineer, Julio Gonzalez, and of course, my cohost, Frank Abagnale. Be sure to find us on Apple Podcasts, Spotify, or wherever you listen to podcasts. For AARP - The Perfect Scam, I'm Julie Getz.
(MUSIC SEGUE)
END OF TRANSCRIPT
Hackers are thought of as villains who use their advanced computer skills to gain unauthorized access to data and wreak havoc. But “ethical” or “white hat” hackers help companies protect themselves against attack. These information security experts use the techniques employed by malicious hackers to reveal real-world vulnerabilities that could result in a hack. Ethical hacker Jason Glassberg is a founder of a company that has been hired by Fortune 500 companies to hack into their systems and expose weaknesses. On this episode of the podcast, Jason discusses his work and the emerging technologies hackers are using to scam companies and individuals.
TIPS: If you think you’ve been a victim of a scam or would like to report fraud call The Fraud Watch Network Helpline at 877-908-3360. Anyone can become the victim of a scam, it’s important to be vigilant and know your vulnerabilities. For instance, if you are looking for a job you are more vulnerable to a work-at-home scam.