AARP Hearing Center


What if we had a key to our computers that was more secure than a password, something that no one could steal or replicate? We already do, and it's you. It's part of a science called biometric authentication. Technology companies are developing tools that use fingerprints, voice recognition, eye scans and facial recognition, and even a quick analysis of your physical behavior — the way you tap the keyboard or move your mouse — to serve as a gate to your accounts or an alert that an unauthorized user has gained access. Here's a look at some of the technologies soon to replace — or augment — your passwords.
Facial recognition
Some flagship Android phones have been enabled with facial recognition tools since 2011, though the early software was insecure — a mere photograph of the correct face could often crack into accounts. Now, with Apple's Face ID for the most advanced iPhones and iPads, facial recognition has been rolled out en masse like never before, and it's more advanced and secure.
The popularity of this tech can be attributed to a simple factor: Nearly all devices today — phones, tablets, computers — have cameras. “A single image can be sent to our servers and then encoded into an algorithmic array of numbers to verify and do recognition on a face,” says Stephen Moore, chief scientific officer for Kairos, a leading facial recognition company.
The downside? Not all companies are scrupulous about who they'll share or sell your data to. Last year, for example, Amazon pitched its facial ID tech to the U.S. Immigrations and Customs Enforcement, raising concerns about security. As companies make deals with the government, cops can run facial identification scans on people driving down the road or walking by on the street.
Body movements
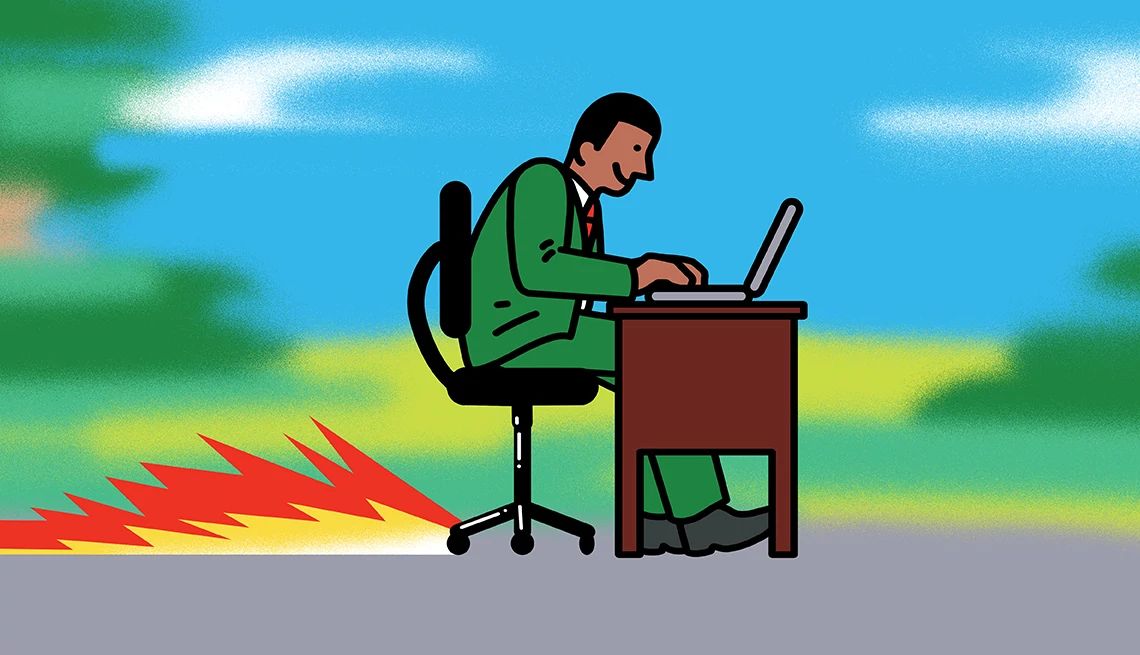
The way you use your devices — the precise way you swipe at your smartphone screen, the angle at which you hold it, your typing speed, how you move your mouse, and even the way you scroll down a screen — is unique to you.
Track this over time, and patterns of behavior emerge. Some cutting-edge apps and websites can track your computer behaviors as a means of continuous authentication. “When you log on to a site, you're jumping through a single hoop to get authenticated with a password,” says Jordan Blake, vice president of products for BehavioSec, a behavioral biometrics company based in San Francisco. “After that, they tend to leave you alone; there's not really additional authentication. With this next generation, instead of one secure door at the beginning of a session, we continue to watch you the entire time.”





























































More From AARP
13 Ways to Protect Yourself From Fraud
Learn how to lower your risk and keep criminals at bay
Experts Share Latest Fraud-Fighting Tactics
Law enforcement officials answer questions and reveal trends